Ready for a fresh day of Cyber horrors? Me neither!
Ready for a fresh day of Cyber horrors? Me neither!
Oh well, here you go: https://opalsec.ghost.io/daily-news-update-wednesday-april-2-2025-australia-melbourne/
Here's a few of the key items to be aware of:
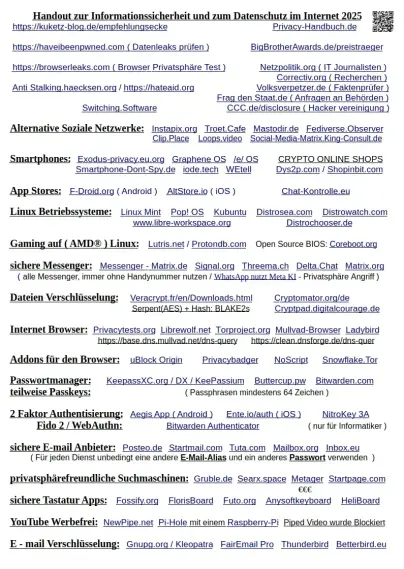
 Palo Alto GlobalProtect Scans: Observed a significant spike in scans targeting Palo Alto Network GlobalProtect login portals, possibly prior to new exploit releases. Time to audit those logs!
Palo Alto GlobalProtect Scans: Observed a significant spike in scans targeting Palo Alto Network GlobalProtect login portals, possibly prior to new exploit releases. Time to audit those logs! 
 China as Top Cyber Threat: Gen. Paul Nakasone (former NSA/Cyber Command Head) highlights China's unprecedented cyber activities, including malicious code in critical infrastructure and rapid exploitation of vulnerabilities. It's time to rethink our defense strategies!
China as Top Cyber Threat: Gen. Paul Nakasone (former NSA/Cyber Command Head) highlights China's unprecedented cyber activities, including malicious code in critical infrastructure and rapid exploitation of vulnerabilities. It's time to rethink our defense strategies! 
 North Korean IT Worker Expansion: North Korean "IT warriors" are infiltrating European companies, using fake identities to secure remote work and fund their regime. Stay vigilant and double-check those remote hires!
North Korean IT Worker Expansion: North Korean "IT warriors" are infiltrating European companies, using fake identities to secure remote work and fund their regime. Stay vigilant and double-check those remote hires! 
 Identity Flaws in Breaches: A new report indicates 60% of incidents involved an identity attack, with compromised valid accounts being a top initial access vector. Focus on robust MFA, least privilege, and AD security!
Identity Flaws in Breaches: A new report indicates 60% of incidents involved an identity attack, with compromised valid accounts being a top initial access vector. Focus on robust MFA, least privilege, and AD security! 
Read the full post for all the details and more actionable insights, and if you want all this straight to your inbox, you're in luck!  https://opalsec.ghost.io/daily-news-update-wednesday-april-2-2025-australia-melbourne/#/portal/signup
https://opalsec.ghost.io/daily-news-update-wednesday-april-2-2025-australia-melbourne/#/portal/signup