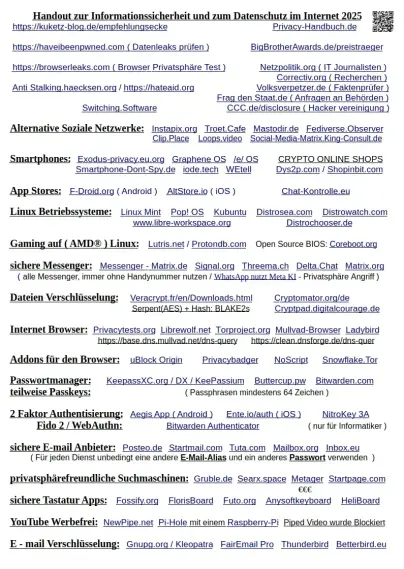
Meine Datenschutz und Privatsphäre Übersicht 2025, für die Allgemeinheit
Teilen erbeten

als PDF:
https://cryptpad.digitalcourage.de/file/#/2/file/NdmBgSYkRCto8B+JmJkE9mQ4/
#DSGVO #TDDDG ( #unplugtrump )
#Datenschutz #Privatsphäre #sicherheit #Verschlüsselung
#encryption #WEtell #SoloKey #NitroKey #Email #Cybersecurity #Pixelfed #Massenűberwachung
#Google #Metadaten #WhatsApp #Threema #Cryptpad #Signal
#Hateaid #Cyberstalking #Messenger #Browser #Youtube #NewPipe #Chatkontrolle #nichtszuverbergen #ÜberwachungsKapitalismus #Microsoft #Apple #Windows #Linux #Matrix #Mastodon #Friendica #Fediverse #Mastodir #Loops #2FA #Ransomware #Foss #VeraCrypt #HateAid #Coreboot #Volksverpetzer #Netzpolitik #Digitalisierung #FragdenStaat #Shiftphone #OpenSource #GrapheneOS #CCC #Mail #Mullvad #PGP #GnuPG #DNS #Gaming #linuxgaming #Lutris #Protondb #eOS #Enshittification
#Bloatware #TPM #Murena #LiberaPay #GnuTaler #Taler #PreppingforFuture
#FediLZ #BlueLZ #InstaLZ #ThreatModel
#FLOSS #UEFI #Medienkompetenz